Project 5: Source-Based Package Build System (Like Gentoo’s Portage)
A system that compiles packages from source with customizable build flags, USE flags, and dependency tracking.
Quick Reference
| Attribute | Value |
|---|---|
| Primary Language | Python |
| Alternative Languages | Bash, Rust, Go |
| Difficulty | Level 3: Advanced (The Engineer) |
| Time Estimate | 3-4 weeks |
| Knowledge Area | Build Systems, Package Management |
| Tooling | Portage, pkgsrc, autotools |
| Prerequisites | Strong shell/Python, understanding of compilation |
Goal: Implement a source-based build system that fetches, configures, builds, installs, and tracks packages with configurable flags and dependency logic. You will understand how recipes, build sandboxes, and optional features create a flexible distribution model.
What You Will Build
A system that compiles packages from source with customizable build flags, USE flags, and dependency tracking. Gentoo’s Portage is the reference model for this approach.
Why It Matters
Source-based package systems expose the entire build pipeline, from source retrieval to compile-time options. This teaches build isolation, configuration management, and dependency modeling at a depth that binary package managers rarely require.
Prerequisites & Background Knowledge
Essential Prerequisites (Must Have)
- Comfort with compiler flags and build systems
- Basic Python or shell scripting
- Understanding of dependency graphs
Helpful But Not Required
- Familiarity with Gentoo ebuilds
- Experience with sandboxing or chroot
Self-Assessment Questions
- Can you explain what a build recipe is?
- Do you know why sandboxing is required during builds?
- Can you reason about optional dependencies?
Core Concept Analysis
Recipe Format
You need a recipe format that defines source URI, dependencies, patches, build steps, and install paths.
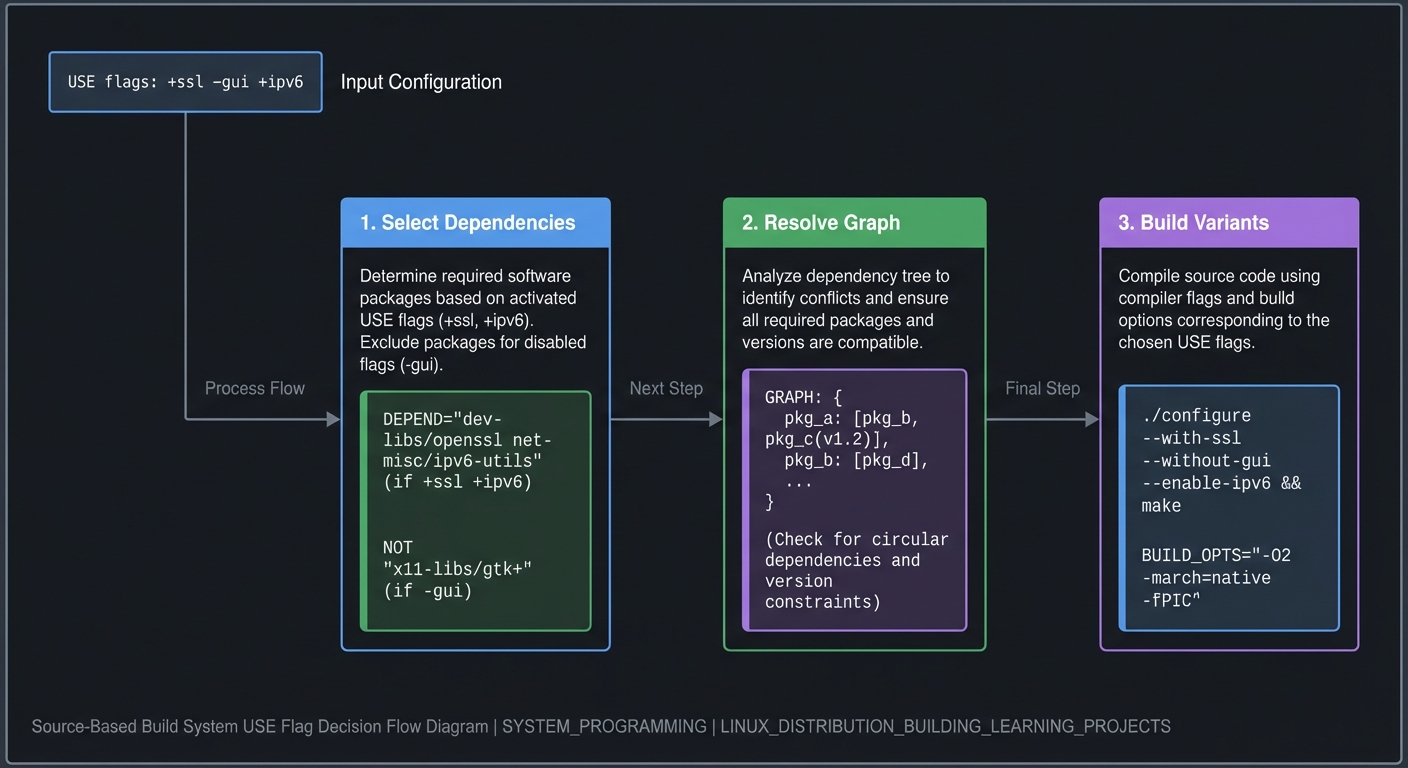
USE Flags (Optional Features)
USE flags toggle optional dependencies and compile-time features. They require conditional dependency logic.
Build Sandbox
Builds must be isolated from the host to prevent contamination and ensure reproducibility.
Slotting and Versions
Slotting allows multiple versions of a package to coexist. Your system should handle version conflicts predictably.
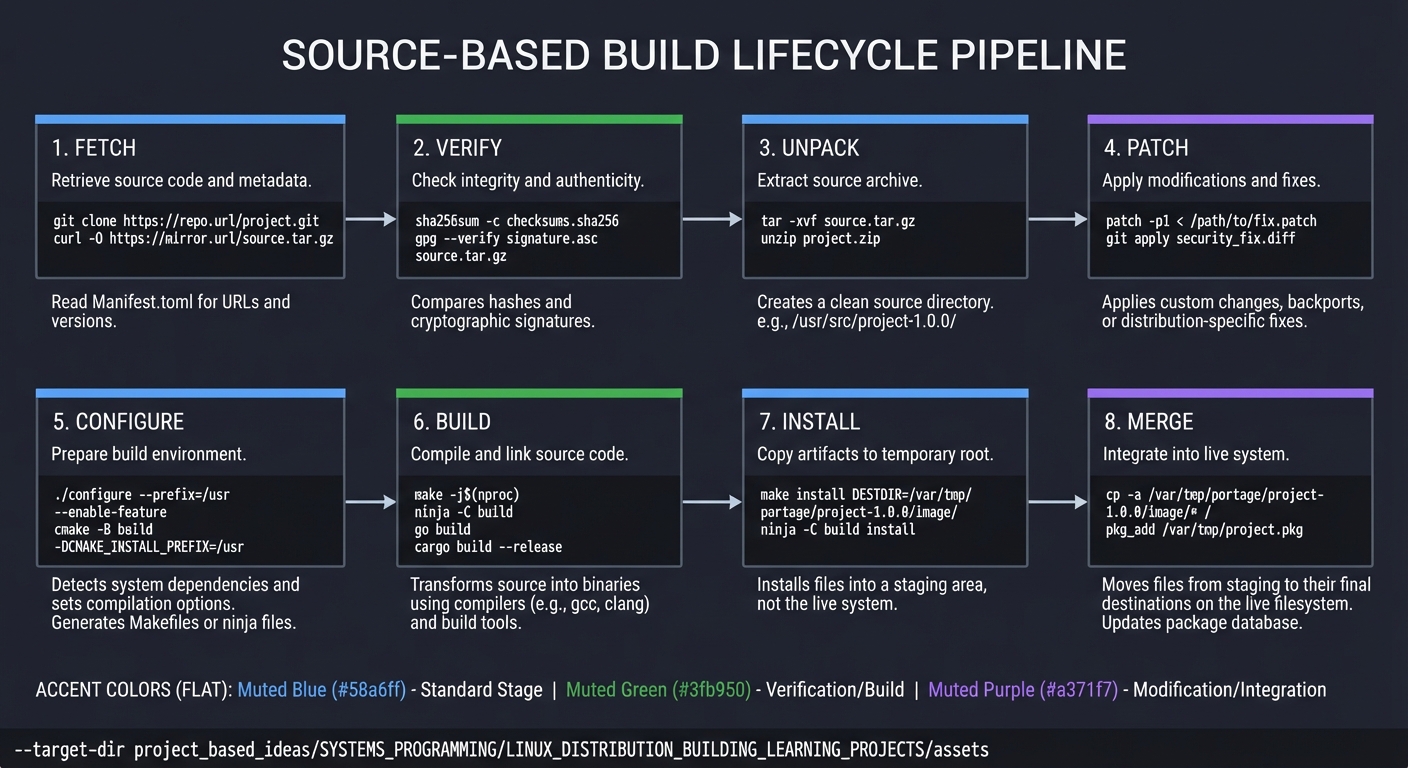
Build Lifecycle (ASCII)
fetch -> verify -> unpack -> patch -> configure -> build -> install -> merge
USE Flag Decision Flow (ASCII)
USE flags: +ssl -gui +ipv6
|
v
select deps -> resolve graph -> build variants
Success Metrics
- Recipes are deterministic and reproducible.
- Builds are isolated and do not write outside the sandbox.
- Optional features produce correct dependency selection.
Implementation Guide
Phase 1: Recipe Parser
- Define metadata fields for source, deps, build steps
- Parse and validate recipes
Phase 2: Fetch + Verify
- Download sources
- Verify checksums and signatures
Phase 3: Build Sandbox
- Build inside a chroot or container
- Limit filesystem writes to a staging root
Phase 4: USE Flags
- Implement feature toggles that modify dependency sets
- Propagate flags into build steps
Phase 5: Install + Merge
- Install into a staging root
- Merge into the live filesystem with ownership tracking
Milestones
- Milestone 1: Simple recipe builds a hello package
- Milestone 2: Dependency resolver handles optional flags
- Milestone 3: Sandbox prevents writes outside staging
- Milestone 4: System supports multiple versions safely
Real-World Outcome
You can show a full source build session with optional flags:
$ spkg build nginx --use "+ssl -debug"
Resolving deps...
- openssl (enabled by +ssl)
- pcre
Fetching sources...
Verifying checksums...
Configuring with CFLAGS='-O2'
Building...
Installing to staging...
Merging into /usr...
Done.
The Core Question You Are Answering
How do you safely and reproducibly compile and install software with optional features?
Concepts You Must Understand First
- Build recipes and standard build phases
- Optional dependencies and constraint solving
- Sandboxing and staged installs
Questions to Guide Your Design
- How will you model optional dependencies cleanly?
- What is the minimal recipe format that still supports patches?
- How will you ensure builds cannot write to the host?
- How will you handle slot conflicts?
Thinking Exercise
Pick a package with optional features (ssl, gui, debug). Model how USE flags change its dependency graph.
The Interview Questions They Will Ask
- Why are staged installs important in source builds?
- How do USE flags impact dependency resolution?
- What makes a build sandbox trustworthy?
- How do you handle multiple versions of the same package?
Hints in Layers
Hint 1
Start with a single recipe format that maps directly to configure/make/install.
Hint 2
Implement staged installs and ownership tracking before optional features.
Hint 3
Add a basic sandbox (chroot or container) and log any forbidden writes.
Books That Will Help
| Concept | Book | Suggested Chapters (use index) | Why This Matters |
|---|---|---|---|
| Build systems | The Linux Programming Interface (Kerrisk) | Process and exec | Understands build steps and environment |
| Make + build | The GNU Make Book (Graham-Cumming) | Basic make rules | Helps model build phases |
| Dependency graphs | Algorithms, Fourth Edition (Sedgewick/Wayne) | Graphs and DAGs | Supports dependency resolution |
| System isolation | Operating Systems: Three Easy Pieces | Virtualization and isolation | Motivates sandboxing |
Common Pitfalls & Debugging
Problem 1: “Build writes outside staging”
- Why: Missing sandbox rules
- Fix: Enforce filesystem whitelist and fail on violations
- Quick test: Create a fake /etc write and verify block
Problem 2: “Optional deps always pulled”
- Why: Flags not plumbed into resolver
- Fix: Map flags to dependency sets explicitly
- Quick test: Build with flags toggled and compare deps
Problem 3: “Conflicting versions”
- Why: No slot or version constraints
- Fix: Add slot metadata and conflict rules
- Quick test: Install two versions of same package
Definition of Done
- Recipe format covers fetch, build, install, and dependencies
- USE flags change dependencies and build steps
- Sandbox prevents host contamination
- Staged installs support atomic merges
- Multiple versions can coexist safely
References
- Main guide:
LINUX_DISTRIBUTION_BUILDING_LEARNING_PROJECTS.md - Gentoo Portage documentation: https://wiki.gentoo.org/wiki/Handbook:PPC/Working/Portage
- GNU Automake manual (Autotools overview): https://www.gnu.org/s/automake/manual/automake.html